I am currently setting up LDAP and I ran into an issue:
Maybe I am missing something here, but basically this scenario should work:
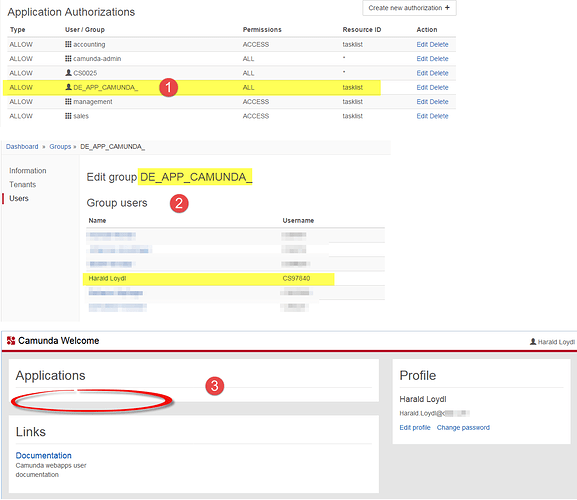
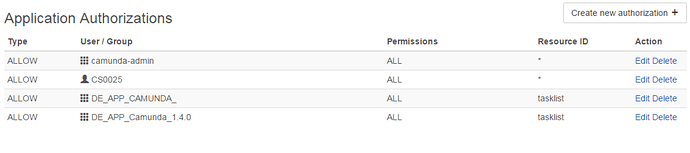
- a LDAP-group is granted permission ALL to resource tasklist. No other authorizartions should interfere here, in the screenshot below you actually see all authorizations configured on the server
- the user CS97840 is member of this group
- Expect: this user can open the tasklist
As you can see from the screenshots (3 - below): the user does not get the tasklist presented, i.e. no permission.
If I grant this user CS97840 the permission directly to the ressource tasklist then it works fine: the user can open the tasklist.
The setup:
Camunda BPM 7.6, shared process engine, Tomcat.
I use a custom LDAP-plugin, which was written by somebody else. This plugin is in production in another region/on another server for some time and I have limited access to the details there.
The LDAP plugin configuration as part of bpm-platform-xml:
<plugin>
<class>com.somecompany.bpm.platform.ldap.LdapIdentityProviderPlugin</class>
<properties>
<property name="serverType">${camunda.ldap.serverType}</property>
<property name="hostNames">${camunda.ldap.hostNames}</property>
<property name="user">${camunda.ldap.user}</property>
<property name="password">${camunda.ldap.password}</property>
<property name="baseDN">${camunda.ldap.baseDN}</property>
<property name="groupPrefix">${camunda.ldap.groupPrefix}</property>
<property name="useSSL">${camunda.ldap.useSSL}</property>
<property name="certificateHostNames">${camunda.ldap.certificateHostNames}</property>
<property name="poolSize">${camunda.ldap.poolSize}</property>
</properties>
<!-- LDAP CONFIGURATION -->
<!-- The following plugin allows you to grant administrator authorizations to an existing LDAP user -->
<plugin>
<class>org.camunda.bpm.engine.impl.plugin.AdministratorAuthorizationPlugin</class>
<properties>
<property name="administratorUserName">CS0025</property>
</properties>
</plugin>
The expressions ${xyz} refer to the Tomcat catalina.properties which are probably not relevant here.
Access to LDAP works fine, I do not see any errors so far.
What can I check or change to make the group authorizations work?
Harald